- Microsoft Authenticator 1password App
- Microsoft Authenticator Passwordless
- Microsoft Authenticator 1password
- Microsoft Authenticator Password Edge
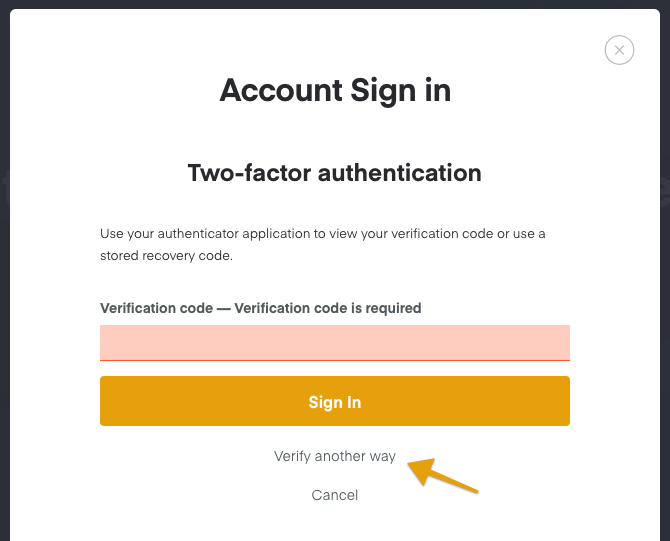
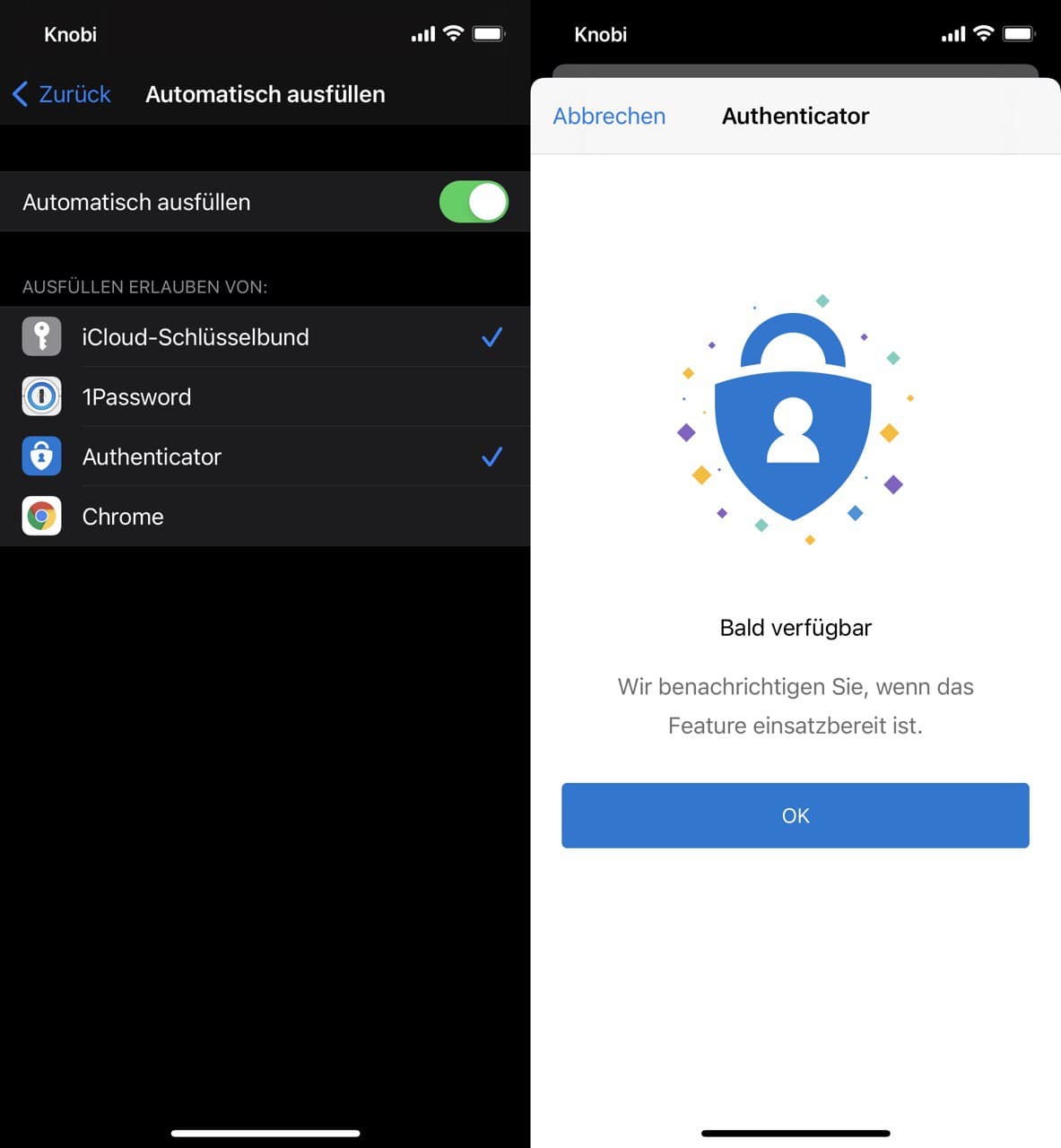
Turn on two-factor authentication for your 1Password account Get an authenticator app. Although 1Password can be used to store one-time passwords for other services where you use. Set up two-factor authentication. Sign in to your account on 1Password.com. Click your name in the top right. Microsoft Authenticator started out as a humble two-factor authentication app, but it was promoted to a proper password manager back in December, complete with syncing to Microsoft Edge.The.
With all the hype surrounding Authenticator Apps, I decided to enable the Microsoft Authenticator on my personal Microsoft account. Microsoft describes the Authenticator as “More secure. Passwords can be forgotten, stolen, or compromised. With Authenticator, your phone provides an extra layer of security on top of your PIN or fingerprint.” As a naturally curious security professional, I am constantly trying out new security services and decided to test Microsoft’s claims.
Microsoft Authenticator 1password App

I downloaded the Authenticator app and added my personal Microsoft account to it. The app asked for my Microsoft password and email verification code. Note that both of these are vulnerable to a simple phishing attack. I completed the registration process and logged into my account several times using the Authenticator app to verify that it worked. It did. I could log into my account without a password.
My assumption, after enabling the app, was that no one else could log into my account without me approving it first through the Authenticator app. It goes without saying that no one should be able to register another Authenticator app on my behalf without me approving it first with the Authenticator app that I already have.
So I asked a friend to try to add my personal Microsoft account to his Microsoft Authenticator app. After he entered my email address I got a push notification on my mobile device. I opened the push notification on my device and selected “Deny” to deny him from continuing. But my friend was faster and selected “use password instead” on his phone moments before I selected “Deny”. My friend was then able to enter my password and email verification code and successfully register his Microsoft Authenticator using my account. Microsoft completely ignored me pushing the Deny button and didn’t provide any feedback that a new Authenticator app was registered on my behalf. Microsoft Authenticator would not prevent a criminal from accessing an account once they have obtained a username and password.
After this experiment we were both able to log into my account, each with our own phones. But what happens if one of us chooses Allow and the other chooses Deny? Apparently first to click wins. If the attacker tries to log in and clicks Approve first, the victim can click Deny but it won’t matter – the attacker will get in and once again – no indication is sent to the victim that someone got in.
Where was the extra layer of security that Microsoft Authenticator claimed? While the Microsoft Authenticator app was easy enough to use (as any Authenticator App), is it simply providing a false sense of security?
Using biometrics and push notifications for security purposes should incorporate many additional layers of security resulting in a dynamic, risk-based approach to authentication and authorization. The best systems carefully assess and correlate a host of indicators and variables from the device and the session in real time to validate the user and revalidate if necessary. In the examples above there were plenty of red flags that should have generated alerts and blocked the imposter before access was provided to the device. If you’re serious about device and system security, continuous adaptive risk should be a foundation to your organization’s IT security infrastructure.

Update: I received a few comments on whether 2FA was enabled or not in my tests above. This is not the point I was trying to make here. Even when 2FA is enabled, attackers can still choose to use Email or SMS as a second factor instead of the Microsoft Authentication App. Both Email and SMS are much weaker in terms of security. I’ll follow up next week with a post explaining how SMS and Email 2FA can be bypassed. My expectation is that once I enable an Authenticator App, attackers should not have an easy way of using SMS or Email instead to login or register another Authenticator App.
Microsoft Authenticator is a security app for two-factor authentication. It competes directly with Google Authenticator, Authy, LastPass Authenticator, and several others. You may run into the app when updating your Microsoft account settings or enabling two-factor authentication there. Alternatively, you may just want to have a TFA available for your own security purposes. Regardless, let’s talk about Microsoft Authenticator and how it works. Hit the button at any time to download the app. You can also find the iOS version by clicking here. This entire guide works for both the iOS and Android versions of the app.
What is Microsoft Authenticator?
Microsoft Authenticator is Microsoft’s two-factor authentication app. It originally launched in beta in June 2016. The app works like most others like it. You log into an account and the account asks for a code. This app generates those types of codes. It’s extremely useful for quick sign-ins, it works cross-platform, and it’s faster than email or text codes.
You can also use the app for no-password sign-ins for your Microsoft account. The app also features multi-account support, and support for non-Microsoft websites and services.
What is two factor authentication and how do you use it?
How does Microsoft Authenticator work?
The app works like most other authentication apps. It generates a string of numbers on a rotating basis of about 30 seconds. In other words, it generates a six digit code every 30 seconds. You simply log into your app or service like normal. The site eventually asks for the two-factor authentication code. Go into the Microsoft Authenticator app to receive those codes.
Microsoft Authenticator Passwordless
It works a little differently on Microsoft accounts than non-Microsoft accounts. You can actually just use the codes in this app to log in without a password for your Microsoft account. However, on all other account types (Facebook, Google, etc), you have to login with your username and password before you can add in the code.
Microsoft supports any website that uses the TOTP (time-based one time password) standard. Thus, the app can continuously generate codes and you use them as needed. This is different from the HOTP standard where a code is generated specifically for you a single time. Sites that use this method, such as Twitter and most likely your banking app, cannot use Microsoft Authenticator.
How to use Microsoft Authenticator:
The app setup is rather easy. Let’s go over setup with your Microsoft account. Simply download the app and open it to begin the tutorial.
Setup for Microsoft accounts:
- Log in with your Microsoft account credentials in the Microsoft Authenticator app. This should be your first prompt upon opening the app for the first time. Simply select “Personal account” or “Work or school account” to log into your Microsoft account.
- After a successful login, you have to authenticate the sign in with a code. You can have it send via text, email, or another method.
- That’s it! Once you input the code, the app is linked to your Microsoft account and you use it for no-password sign-ins. Next time you log in, simply enter your username and then input the code generated by the app.
Setup for non-Microsoft accounts:
This varies from website to website, but the general idea remains the same. It’s a fairly straightforward process. You can prepare the Microsoft Authenticator app for the task by tapping the three dot menu button in the Microsoft Authenticator app and selecting the “Add account” option. From there, select the “Other account” option and prepare to follow the below steps.
- Return to the website where it should ask you if you want two-factor authentication via text and email or with an application. Select the application option.
- You will either see a QR code on your screen or a six digit code. Use the Microsoft Authenticator app to scan the QR code.
- Alternatively, the site may give you a code to enter instead of a QR code. Not a problem! Go back into the app and tap the “Or Enter Code Manually” option on the bottom of the page. Give your account a name first so you know which one it is and enter the code beneath it.
That’s it, really. The Microsoft account setup is something you should only have to do a single time. Meanwhile, you can add whatever online accounts you want by repeating the non-Microsoft account steps on all of your other accounts.
From there, using the app is very easy. You simply log in with your email or username and password on non-Microsoft websites and enter the six digit code from the Microsoft Authenticator app when prompted. Microsoft websites simply need you to add your username and it’ll then ask you for a code from the app. That’s about all this app does and that’s all it’s designed to do!
10 best security apps for Android that aren’t antivirus apps
Microsoft Authenticator 1password
10 best two-factor authenticator apps for Android
Microsoft Authenticator Password Edge
If we missed anything about Microsoft Authenticator, let us know about it in the comments! You can also click here to check out more tutorials!

